Is one of your IoT devices inviting hackers in?

Are you sure every small device across your network has the right protection to keep hackers out? Easily forgotten, we take a look at how to keep your IoT environment safe, right down to the oldest, most primitive device.
Real-world example: Unsecured sensor caused data breach
Two years ago, a company suffered a data breach when hackers infiltrated their Wi-Fi network. The surprising entry point? A simple fish tank temperature sensor connected to the network. This sensor lacked security monitoring, so its unauthorised access went unnoticed. Hackers exploited the sensor’s network connection to reach the main database, stealing sensitive customer information.
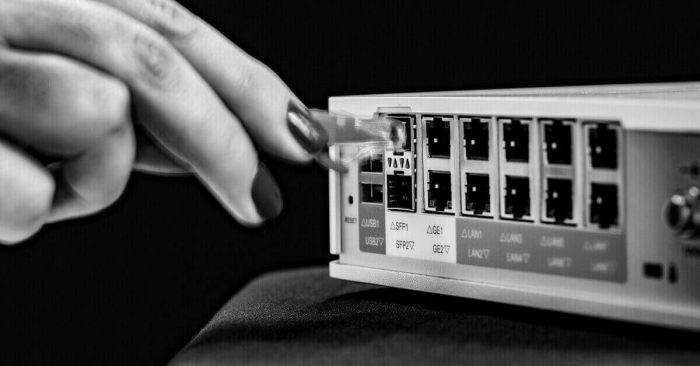
Unintelligent devices need smarter network protection
Many businesses rely on specialised, non-intelligent equipment like security cameras, motion sensors, or temperature gauges. These bespoke systems are often expensive and rarely updated. While they perform their core function well, they lack the ability to detect hacking attempts.
This is where network-level intelligence comes in. Modern networks (like SASE) can analyse data traffic and device behaviour to identify anomalies in even basic devices. For instance, an unintelligent security camera might simply transmit images or send signals. But a smart network can analyse that data. If the camera starts sending traffic to a suspicious location or shows a spike in data transmission, IT can investigate and remove it from the network if necessary.
Cyberattacks can lurk within your walls
While we often hear about large-scale attacks from external sources, internal threats shouldn’t be ignored. Any device on your network can be a vulnerability. Common office equipment like:
• Security cameras
• Wi-Fi routers
• Printers
• Sensors (smart or basic)
Why are these devices vulnerable?
• Weak security protocols: Many devices, especially older ones, were built with outdated security standards.
• Default passwords: Often, IoT devices come with default passwords that remain unchanged, creating an easy target for hackers. Network administrators might not be aware of these weak credentials without proper reporting tools.
• Outdated firmware: Non-intelligent devices frequently lack the ability for over-the-air firmware updates. Manual updates for each device are often neglected, leaving them with outdated firmware and increased security risks.
The answer: AI-powered network protection
Modern network infrastructure can build detailed profiles of each device’s typical traffic patterns. If there’s a change, big or small, in the type or amount of data flowing to and from the device, your IT or security team will be alerted for further investigation.