CEOs wish they’d known this when their network was hacked

Lots of companies are currently leaving the defence of their confidential data up to traditional networks that simply aren’t up to the task. Here are five ways most of today’s networks are leaving the door open to hackers, while also hurting the productivity of the business.
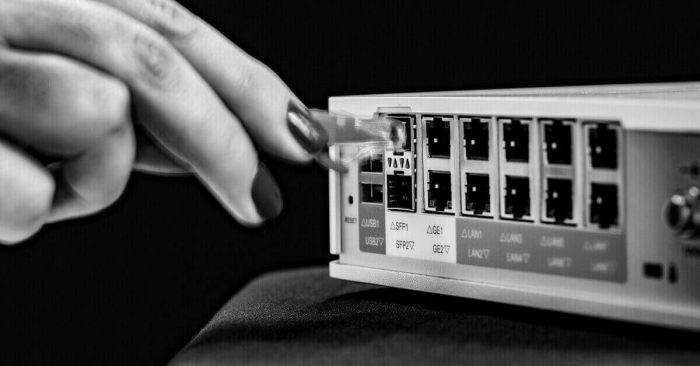
Your whole network is at risk until every device has the latest security patch. (But it doesn’t have to be.)
In a traditional system, your entire network is vulnerable to the latest threat right up until the moment every single ppliance on your network has been security patched. This means sending an IT professional to every single firewall and router, and having them update the firmware individually. In the case of a large organisation, that can take weeks or months to complete. And while you’re waiting for it to happen, you could experience a data breach through any of the unpathched devices.
A tiny, insignificant sensor that’s not adequately protected could be the start of a major data breach.
Two years ago, a complany in the US lost their customers’ critical financial data through a direct attack on their Wi-Fi network. The breach started in the most unlikely way: through the temperature sensor in a fish tank on their premises. The sensor was connected to the network, but being a simple reporting device, it wasn’t monitored for attacks. So when it was accessed in an unauthorised way, the company’s IT team wasn’t alerted. Hackers realised they could find their way into the company’s main database through the tank sensor, and once they were in, they had unfettered access to the personal and financial details of the company’s clients.
One person’s personal cloud storage could lead to a major data breach (except if you have SASE).
Employees these days expect to run their personal apps on devices provided by their company. A typical user might run WhatsApp on their phone, and Google Drive on their company laptop to access personal files.
This opens up your business to significant risk. Whether a disgruntled employee decides to move confidiential company files across to their own cloud storage drive, or an employee transfers data from a business folder to a personal cloud folder in error, the result is the same. In either scenario, critical data can end up outside your company’s safe environment, and out of your control. Until now, the only way to prevent this was a blanket block of all non-work applications.
Giving your remote workers fast access doesn’t have to mean compromised security.
Traditional networks send data packets all the way to the head office or data centre (and back again) so it can pass through company firewalls. This means that to keep everything safe, speed takes a huge hit. Often, remote workers will simply bypass this security round-trip so they can work fast. And that means that people working away from the main offices can put your data’s safety at risk. Your remote workers might be compromising your private data right now.
You don’t have to have a planned outage every time you update your network security.
In traditional networks, every time any piece of hardware is updated with a security patch, a scheduled outage is needed. This means bringing down part of the network for each piece of equipment. Even though this can be planned, it usually means disruption to people or systems which depend on network access.